|
Listen To The Article
|
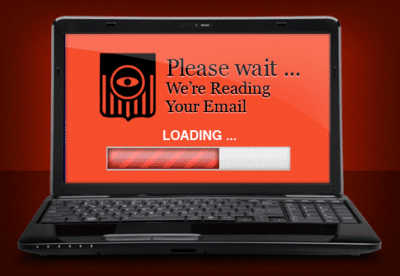
CISPA could give companies the right to read your email and monitor your online activity without a warrant.
You might not have heard about CISPA yet, but if the Fourth Amendment is important to you, then the time to fight back against the big brother intrusion is now. Also known as the Cyber Intelligence Sharing and Protection Act, CISPA is a law supposedly written to protect America from cyber threats. It sounds like a good thing on its face, but a closer look into the text of the legislation reveals an attack on privacy protections.
The cyber security bill gives new powers that would potentially derail Fourth Amendment protections in America. CISPA allows “self-protected entities” and “cyber security providers” the ability to peek at private online activity without a warrant. While the online security providers are not permitted to be governmental entities, do not breathe a sigh of relief just yet. Loopholes in the self-protected entities description portion of the bill do not reportedly boast such an exclusion of big brother tactics.
The intent of the Cyber Intelligence Sharing and Protection Act was supposedly to give specific companies the power to obtain possible cyber threat activities without a warrant. Companies such as Facebook and McAfee would be able to access user accounts without permission or even notification. Finding and thwarting such attacks should be considered a matter of national security, but circumventing Fourth Amendment rights is not an acceptable way to get the job done.
Even though the protections Americans enjoy under the Fourth Amendment limits the ability of the government to utilize the new powers offered by CISPA, potential Constitutional infringements are still possible. The legislation reportedly grants the government “broad immunity” for any decisions made based upon cyber threat information.
#CISPA basically ends warrants and other forms of legal mandate, think of it as an indefinite wiretap on everyone. #CISPABlackout
— Anonymous (@YourAnonNews) April 22, 2013
The act could allow governmental agencies the ability to override the Privacy Protection Act, an act that protects the personal information of individuals used in government records. CISPA could also possibly impede upon the protections offered in the Computer Matching and Privacy Protection Act. (The computer records legislation limits the ability of the government to engage in an automated matching system with governmental records containing citizen information.)
A host of civil liberties groups and Libertarians from around the country have been fighting back against the bill since its inception. Also known as HR 3523, CISPA was introduced by Republican Representative Michael Rogers in 2011. The legislation did not pass the Senate the first time through. Representative Rogers and Democratic Representative Dutch Ruppersberger reintroduced the cyber security bill in February.
Excerpts from the bill:
- The Director of National Intelligence shall establish procedures to allow elements of the intelligence community to share cyber threat intelligence with private-sector entities and utilities and to encourage the sharing of such intelligence.
- The procedures established under paragraph (1) shall provide that classified cyber threat intelligence may only be shared by an element of the intelligence community with certified entities or a person with an appropriate security clearance to receive such cyber threat intelligence. The information can also be shared consistent with the need to protect the national security of the United States; and used by a certified entity in a manner which protects such cyber threat intelligence from unauthorized disclosure.
- The Director of National Intelligence shall issue guidelines providing that the head of an element of the intelligence community may, as the head of such an element considers necessary, to carry out this subsection: grant security clearance on a temporary or permanent basis to an employee or officer of a certified entity and similarity grant permission to use appropriate facilities, and expedite the security clearance process for an entity or individual in an effort to protect national security.
- Cyber security bill also allows providers to identify and obtain cyber threat information to protect the right and property.
- Information shared with the Nation Cyber Security and Communications Integration Center of the Department of Homeland Security is subject to the use and protection of information requirements under paragraph, the head of a department or agency of the Federal Government receiving cyber threat information shall provide such cyber threat information to the National Cyber security and Communications Integration Center of the Department of Homeland Security.

Cyber security should not come at the expense of 4th Amendment protections.
Opponents continue to rightfully maintain that CISPA would allow Internet records and other personal correspondence, such as emails, to be handed over to the government at any time. However, many companies have voiced their support of CISPA. Companies like Time Warner Cable, AT&T, Google, Verizon, Facebook, IBM, and Intel have all come out in support of the warrantless search legislation. A statement released by certain supporters reads: “If the government learns of an intrusion or other attack, the more it can share about that attack with private companies and the faster it can share the information, the better the protection for users and our systems.”
Granted, cyber threats are a serious concern for both the government and many in the prepper and survival community. Recent stories about the alleged activities of Chinese hackers clearly illustrated how dangerous online attacks could be for America. If a hacker can successfully make entry into the control system of our power grid, life as we know it would cease – at least for a while. Hacking into the computer system at the Pentagon could prove equally as deadly.
While monitoring and responding to such threats should be an integral part of our overall national security plan, we simply cannot throw the Fourth Amendment out the window. Cyber threats require quick action, but a warrant should still be necessary.
We cannot allow our concerns about terrorism and cyber hackers to turn into an overwhelming fear that prompts a shredding of the Constitution. Perhaps the most concerning part of the CISPA legislation is the vagueness of the text. A law which could impact protections offered by the Fourth Amendment should be extremely precise, leaving not a single line item up for interpretation.
It will be an uphill battle to prevent CISPA from infringing upon our Fourth Amendment rights at this point. Not only has the bill already passed the House, it has supporters with extremely deep pockets. The big name companies that support the bill spent around 140 times more money during the vote battle than opponents. The primary reasons the tech companies are hopping on board the CISPA movement is to limit their own liability in the when sharing user information. If CISPA passes the Senate, the service providers and websites no longer have to worry about being sued by users for turning their online activity records over to governmental agencies.
Although United States citizens want a safe and protected nation, patriots are simply unwilling to step on the Constitution to achieve such a goal. The Fourth Amendment protects Americans from unreasonable search and seizure of their person, effects, papers, and home. If there is probable cause to suspect a cyber security threat is unfolding, then a warrant should be obtained. If we bend and twist and chip away at the rights which serve as the foundation of the America, the country CISPA was created to protect will cease to exist.
 Off The Grid News Better Ideas For Off The Grid Living
Off The Grid News Better Ideas For Off The Grid Living



